How Secure Is Tap To Pay?
Now Playing
How Secure Is Tap To Pay?
Transcript
696 segments
- I'm here with MKBHD,
and we're gonna try to steal $10,000 from his locked iPhone.
- Really hope it doesn't work.
Really hope it doesn't work.
- I'm gonna get you to put that phone down
on top of this device.
- [Marques] Okay. - Just put it down there.
- Just put it on like a, all right.
- I feel like I'm a bit of a magician,
but I'm like- - Yeah.
- I haven't changed anything, right?
- Okay. Yeah.
- It's still locked. - It's locked.
- Nothing else. - Yeah.
- This is just a regular payment terminal.
- Yeah. - Nothing weird about that.
- Seen these.
- And we'll start with a little, like, maybe 100.
No, maybe $5?
Let's start with something like-
- Yeah, five. Five. - Start with five.
- That sounds great. - Yeah. Five bucks.
Do you think that we can take,
like, will we be able to get this out of your phone?
- I hope not, but I kinda feel like you will.
Let's see.
- So, now I'm gonna charge $5 on this device.
Your phone's still locked, right?
- Yep.
- I haven't done anything. - It's like a David Blaine.
- [Henry] It's like the nerdiest David Blaine.
- Yeah. (chuckles)
- Sweet, so.
Just try to tap. We'll go.
(phone chimes)
- What just happened on my phone?
Approved? Whoa, whoa, approved.
(coins clinking) So, okay.
I heard something happen on my phone
while you tapped this on this.
- Yes.
We got a little receipt for you.
- Credit verified on device, $5.
So, I'm gonna check my phone.
Ah, oh, I have a new $5 charge.
And it's time stamped right now.
I don't like that at all.
So, that's concerning.
Oh, so my phone had to be on this thing?
- [Henry] Yes.
- Did it have to be on this thing?
Or like, near it, I guess?
- So the way, well, I could explain how it works-
- Yeah. - But maybe before that,
$5, it's not very much. - Yeah.
- Do we want to try upping it a bit?
- I...
- I'm gonna enter a slightly larger amount.
- Careful. Careful with that.
Careful, careful.
That's a lot of zeros. Careful with that.
Oh my God. Okay.
- Do you even think it's possible? Firstly, $10,000.
- I mean, the credit, the limit on the card is above that.
I don't know if Apple Pay will let you do that.
- The question is also are you used to spending
this amount of money on this card, you know?
- Not from my phone.
It's like a big screen activity.
- Yeah. - Like, $10,000 purchase,
I gotta be checking everything.
So, yeah, no. This would be unusual.
- Let's see it. Let's see if it works.
Okay, I'm gonna do it again.
- Okay. - We're just,
all we gotta do again.
Put your phone locked.
Phone- - On this device.
- Locked on that device.
- [Henry] Yes, exactly.
And okay, we're gonna start the script again.
Okay.
(suspenseful music)
(phone chimes)
- [Marques] Uh-uh.
(coins clinking)
Uh-uh. No.
- No? (laughs) - It's just green. Approved.
- Print that out. Print that.
(receipt sprinting)
That is crazy.
- Oh my God. So, so, yeah, I'm gonna need that back.
- Yeah. (laughs) - For sure,
I'm gonna need that back.
But also, did that just?
Yeah, wow. It worked.
- $10,000.
- All right. I believe you.
I definitely believe you.
How do we get this back?
We do like a little Venmo or like PayPal?
How do we even? - You know,
do we give it back though? - Reverse the transaction.
I don't even know. Do I call my company?
Yeah, that's crazy. - Yeah, exactly.
You can keep this if you wanna-
- Yeah. - Get it framed.
- Yeah. A receipt of the damage.
I never unlock my phone. I never put in a password.
I never did what I would normally do
to verify a transaction on my phone.
- Yes. - It just happened
to be on top of that.
- So, how did we do it?
Well, we teamed up with two cybersecurity experts,
Professors Ioana Boureanu and Tom Chothia.
And we went to visit them at the University of Surrey,
where they ran us through a unique hack that they developed
to bypass the phone's lock screen and then to drain funds
from inside its mobile wallet.
- Without unlocking my phone is the real magic part.
That's crazy.
- And the craziest thing of all is that this hack
was made public back in 2021.
So, people have known that it's possible
to take money from locked phones in this way for five years.
So, what kind of amounts does this?
- The only limit is how much someone has
in their bank account.
(suspenseful music)
- Yet the loophole still hasn't been fixed.
So, how does it work?
Well, whenever you use Tap to Pay, your phone and the reader
exchange information about the transaction.
But they send this information through the air
by a shared magnetic field,
so we can intercept the communication and alter it.
All we need to do is to insert our own devices
in between the phone and the reader.
First, we tap Marques's phone against this.
It's an NFC device called the Proxmark.
To Marques's phone,
the proxmark looks like a typical card reader.
So, it happily sends over its transaction data.
That proxmark then sends that data straight to our laptop,
where we run a Python script to modify it.
Next, the laptop sends the data to our burner phone,
which I tap on the actual card reader.
To the reader, my phone looks just like Marques's.
So, both Marques's phone and the card reader
think they're talking directly to each other,
when in fact all their communication
goes through our series of devices.
This is a classic man-in-the-middle attack.
Now, getting in the middle to intercept the data
is actually the easy part.
The hard part is what you need to do to that data
to trick the phone and the reader
into authorizing the transaction.
See, to actually steal money using this attack,
you have to get past three layers
of defense on both systems.
And to do that, we have to tell three lies.
Two to the phone, and one to the reader.
So, the first layer of defense is the simplest.
The phone is locked.
And in an ordinary transaction,
you have to unlock your phone to pay.
But this is no ordinary transaction.
So, you know, if you ever go to the subway,
there's a feature that Apple's created where you know,
when you walk through,
they don't want a bunch of people lining up
and having to unlock their face.
And you know, maybe they're wearing a coat
and glasses and stuff. - Oh. Express Transit Mode.
- Apple introduced express transit mode in 2019
to let you make transit transactions
without having to unlock your phone.
The way this works is that the payment terminals
on the subway or on the bus broadcast a message
that identifies them as a transit terminal.
Then, when you tap your phone to pay,
it looks for whatever card is in the transit slot
of its mobile wallet and it pays without needing to unlock.
This is super convenient, but we can also abuse it.
- We found out how this worked
by going to the London Underground
with our laptops and our equipment,
and actually scanning the signals
and seeing what the gate was saying to the phone.
And that's how we discovered this code the gate send
which unlocked the phone.
- We used the proxmark to broadcast that same code,
which fools Marques's phone into thinking
that it's a transit reader.
So, when we tap Marques's phone against the proxmark,
it's now expecting to receive another message
with the details about the transit transaction.
Here's what that message would typically look like
in binary code.
Each of these bits carries important information
about the transaction.
Now, the important part of this message for us is this bit.
An authentic transit transaction would have a 1 right here.
This tells the phone that the reader may be offline.
Like if it's underground on the subway.
In which case the phone would need to send
an extra layer of authentication.
So, when Marques's phone receives the transaction request
from what it thinks is a transit reader,
it's gonna be expecting that value to be set to 1.
But in reality, the device sending the request
is our retail reader, and this reader is online,
which means that that bit is currently set to zero.
Therefore, to trick the phone
into accepting the transaction,
we intercept the message from the reader,
pass it through our computer,
and we change that 0 to a 1.
So by the time the message gets to Marques's phone,
it looks like a transit transaction.
As this communicates through our computer,
we're convincing the phone
that it is in fact talking to a transit terminal.
But now there's a second line of defense we need to break.
With this first lie,
we bypassed the need to unlock the phone.
And we can now trick it
into making small payments of a few dollars.
Kind you'd expect on the subway.
But if we suddenly went and asked the phone for $10,000,
well, its guard would go way back up.
After all, it's pretty unusual for a transit reader
to ask for such a large amount of money.
So, this activates a second layer of defense.
Customer verification.
On contactless payments like this,
there are two categories of transaction.
We got high value and low value.
Any transaction that's classified as high value
requires additional verification from the customer.
For example, in the UK, most banks require a pin
or a fingerprint or facial recognition
for any transaction over 100 pounds.
So, for us to get this $10,000 payment through
without customer verification,
we need to trick the phone into thinking
that $10,000 is in fact a low value transaction.
And that's actually surprisingly simple.
That's because to determine
whether the transaction is high value,
Marques's phone doesn't actually look
at the numerical value of $10,000.
It just looks at another single bit of information
in the transaction data.
A 1 here means high value and 0 means low.
The reason for this is that the boundary
between high and low value varies from country to country.
And of course,
different countries operate in different currencies.
So, a simple label allows the flexibility
to deal with these variations.
And it allows the limits to be changed
without the banks needing to issue new cards.
So, all we need to do
is intercept the message from the reader,
flip that bit to a zero,
and then the phone will believe
that this transaction is low value
even though it's for $10,000.
Then, when the phone receives our request
for a $10,000 transaction,
it doesn't ask for customer verification.
It just goes ahead and authorizes the transaction.
Now, you might be asking,
why is this data so easy to tamper with?
And we'll get to that in just a minute.
But we have one final security check to overcome.
See, with these first two lies,
we bypassed unlocking the phone
and then tricked it into making a high value transaction
without asking for verification.
So, the phone is fully convinced
and it's ready to make the payment.
But we still need to convince the reader
that the transaction's valid.
And this is where our third lie comes in.
When Marques's phone replies,
it says it's approved the $10,000 transaction.
But it also says that it hasn't asked
for customer verification.
No pin, no fingerprint, no facial recognition.
But if the reader sees this, it'll reject the transaction
because it knows that the $10,000 payment
it originally asked for is high value.
It should therefore require customer verification.
So, now we need to trick the reader
into thinking that the customer has verified the payment.
So, we intercept the response from Marques's phone
and look for the bit of information
that says customer verification hasn't been done.
Then we change it to say that the payment has been verified
by flipping this 0 to a 1.
Now, the reader's happy.
It forwards the information onto the bank,
and the bank authorizes the payment.
After all, it sees a transaction that's been verified
by the customer on their device.
(upbeat lively music)
(notification beeps)
Green approved.
(coins clinking)
- That is crazy.
- Verified on device? - Yeah, verified.
- You didn't, you didn't verify it.
- Right.
- So, why isn't all this information encrypted?
That would make it impossible to secretly tamper with.
Well, the way the phone and reader communicate
has to be compatible with thousands of different devices,
which would be impossible to update all in one go.
So for that reason, the information we've looked at so far
is just sent across unencrypted.
Even still, phones, readers and banks
all have checks in place to make sure
an attack like this can't happen.
And normally, it can't.
Except if you happen to use a specific type of phone
and a specific type of card.
Because when you combine them in this particular scenario,
they create a loophole.
So, our hack relied on a specific phone
and credit card combination.
And we also use a sophisticated method
developed by cybersecurity experts.
But hackers or scammers online,
well, they don't need to be that smart.
Often they can just buy information to target you.
When I started working at Veritasium,
I was on a work trip to go meet Derek for the first time.
And I got an email from somebody was saying he was Derek
asking for my phone number.
That made a ton of sense.
I was leaving the airport.
So, I just responded by sending my phone number.
I immediately was like, "Wait, let me look at that."
I checked the email. Not Derek.
Of course, for the next few months
I was just getting scam call after scam call.
That's one way they can get you. I felt like an idiot.
But it's not just scam calls like that.
I've also had that feeling
after news of a major data breach.
I've wondered whether me using some website
has led to my personal information being exposed somewhere
without me even knowing about it.
But you can protect your personal info
with today's sponsor, Incogni.
See, whenever scammers purchase your email, phone number,
and even your home address from data brokers,
Incogni automates the grueling process of requesting
that these data brokers delete your information.
Okay, so I've had this since June 2025.
And since then, we've had 94 different removal requests.
And I really like how you can track the progress
in this dashboard here.
They've estimated that that saved me
70 hours and 30 minutes of my own time
if I were to reach out to these people myself.
And with Incogni's new custom removal feature
in their unlimited plans,
you can point to any specific site
where your information is visible.
And then, one of their privacy agents
will take care of the rest.
So, to take your data off the market today,
go to incogni.com/veritasium
and then use code Veritasium for 60% off.
You can click the link below
or you can scan this QR code to claim that 60% off
and get your personal data off the market.
I wanna thank Incogni for sponsoring this video
about taking money from Marques Brownlee.
And now, let's get back to that thing.
So, which combination of card and phone
make this hack possible?
Firstly, the phone has to be an iPhone.
As we saw earlier, when an iPhone is deciding
whether to ask for customer verification,
it doesn't look at the numerical value of the transaction.
It only looks at the high value or low value label
provided by the reader.
But other phones don't work that way.
For example, when a Samsung phone goes into transit mode,
it doesn't rely on this low value label from the reader.
It looks at the actual numerical value of the transaction
and it only accepts a payment of $0.
Then it relies on the transport provider
to count up all the times you've used the subway,
and then to send you a bill at the end of the day.
So, if a Samsung phone saw a transit terminal
trying to charge you $10,000 for a single tap,
it would immediately reject it.
But it's not just Apple's transit mode
that makes this hack possible.
You've gotta have one specific type of card
in the transit slot.
- It was truly a design feature that was introduced
by the way you mixed Apple and Visa.
- And the reason that this works with a Visa card,
but wouldn't, with say, a MasterCard
comes down to the different processes they use
to verify transactions.
So, what is it about Visa's verification process
that makes this hack possible?
In a previous video, we saw that any card transaction
relies on a secret cryptographic key
shared by the card and the bank.
When you tap the card or phone onto a reader,
the reader sends across
a long string of transaction details.
The card then applies its secret key to garble that message
into a unique code for the transaction.
The card sends this to the reader,
which the reader forwards onto the bank,
along with the raw transaction details.
The bank then applies its own secret key
to the raw data as well.
And if the output matches the one from the card,
the bank authorizes the transaction.
This is called symmetric cryptography
since the card and the bank use the same secret key.
And this step is required in all transactions.
No matter whether you have a Visa, a MasterCard,
or something else.
But there's actually another layer of security
which MasterCard uses in all of its transactions.
But in this particular case, Visa doesn't.
This layer of security is not between the card and the bank,
but between the card and the reader.
And it's at this step where MasterCard thwarts our attack.
The second step relies on asymmetric cryptography.
So-called because it uses two different keys.
A private key for the card and a public key for the reader.
It starts with the reader sending across
the transaction details to the card just like before.
The card then uses its private key to garble that message
into another long string of digits.
This is the card's digital signature for the transaction.
The card sends this signature back to the reader
along with the public key, which the reader then uses
to verify that the signature came from that specific card
for this specific transaction.
To illustrate how this works,
let's consider a simple example.
The private key and public key both have two components.
N is a shared number.
In this case, let's say 55.
D is the card's private number. Let's say 7.
And E is the public number. Let's say 3.
Now, when the reader sends across the raw transaction data,
it represents it as one long number.
But for simplicity, we'll use a much smaller one.
Let's say 2.
To sign for the transaction, the card or the phone
raises the transaction number, in this case 2,
to the power of its private number, so we get 128.
And then divides this by the shared number, 128 over 55,
which leaves a remainder of 18.
And this is the card signature, 18,
which it sends on to the reader.
Now, the reader needs to know
whether the transaction is valid.
So, it takes the card signature
and raises it to the power of the public number.
Then, it takes the remainder
when you divide by the shared number 55.
And you get 2.
This matches the original transaction data
the reader sent to the card.
The reason this works is that the private and public numbers
are specifically chosen
so that when combined with the shared number,
the public key effectively reverses the operation
of the private key.
And this allows the reader to verify
that the card signature is valid
without ever having seen its private number.
This is based on a type of cryptography called RSA.
In reality, the numbers involved are much larger.
But that makes it incredibly secure
because that makes it virtually impossible
to reverse engineer the card's private key.
And it also means that even a one digit change
in the transaction data will produce a different result
when the reader checks the phone's signature,
in which case the reader won't approve the transaction.
This is a problem because we've modified the data.
The reader's expecting a signature
for a high value retail transaction.
But we intercepted the communication.
So the phone signature
is actually for low value transit transaction.
This wouldn't pass the asymmetric signature check.
But while MasterCard always requires
this asymmetric verification,
which would spot our hack, Visa doesn't.
They only require this signature in certain situations.
Like, when the reader's offline.
For example, when you're underground with no signal,
there's no way for the reader to communicate with the bank
for that first layer of symmetric cryptography.
At least not until it comes back online.
So, during our attack,
we make sure the reader is online the whole time.
That way, it doesn't bother using
the asymmetric layer of security,
which contains the signature that would unravel our lies.
But the funny thing is we've tricked the phone
into thinking it's interacting with the transit reader.
And transit transactions are one of those times
where Visa does require the asymmetric signature,
since the reader could be underground on the subway,
and therefore offline.
So, the phone actually does send across
its signature to the reader,
but the reader doesn't check it.
Because in reality, the reader's online.
So, instead it just relies
on that first layer of security with the bank,
even though if it did check the phone signature,
it would've all the evidence it needed to stop the hack.
(screen whooshing)
So yeah, you go. - Makes sense
that it's that sophisticated
'cause it shouldn't be that easy,
but that still seemed way too easy.
- And Marques was not the only victim.
I thought it was only fair
that I first try it out on myself.
(phone beeping)
- Approved it. - Woohoohoo!
- Yeah, here. You souvenir from the UK from Tom and me.
- Oh, what a lovely receipt for this theft. (chuckles)
And then I got another victim with a bit of a bigger budget.
Our channel has a CFO basically, who lives very nearby.
What we're doing is we're setting it
to be your transit card.
- Okay. - So that means
that if you're in, London you have to use the tube-
- Yeah. - It'll take money
from this card.
Something just happened. - Yeah.
(everyone laughs)
How you feel about that? - Oh my goodness me.
Oh my-
- [Henry] There you go.
- We were just gonna meet for a drink.
That's what, you know, that was the agreement.
- In the real world, say you had your phone in your pocket.
- Yeah.
- I would walk by you-
- Yeah. - Doing this.
And Tom would have this in the shop and pay.
- The easiest way for this to actually be a crime
would be a stolen iPhone.
- [Henry] Sure.
- And then someone goes and spends thousands of pounds.
- So you know, you could buy a car with us.
- Jesus. Yeah, yeah.
Theoretically. Geez.
- Yeah. - Wow.
- I guess from your perspective,
you've revealed all this information publicly
and you're telling us.
We're walking through it in great detail.
How do we stop people from using this for-
Or can we stop people?
Like, whose responsibility is it to stop this?
- Oh, whose responsibility is it is an interesting question.
- Yeah. - But you can stop it
by turning transit mode off.
- Or not turn it off, but not have a Visa card
in transit mode on an Apple.
- Yes.
And you do need to be careful
because as soon as you have a suitable card
in your Apple wallet,
Express Transit Mode is turned on by default.
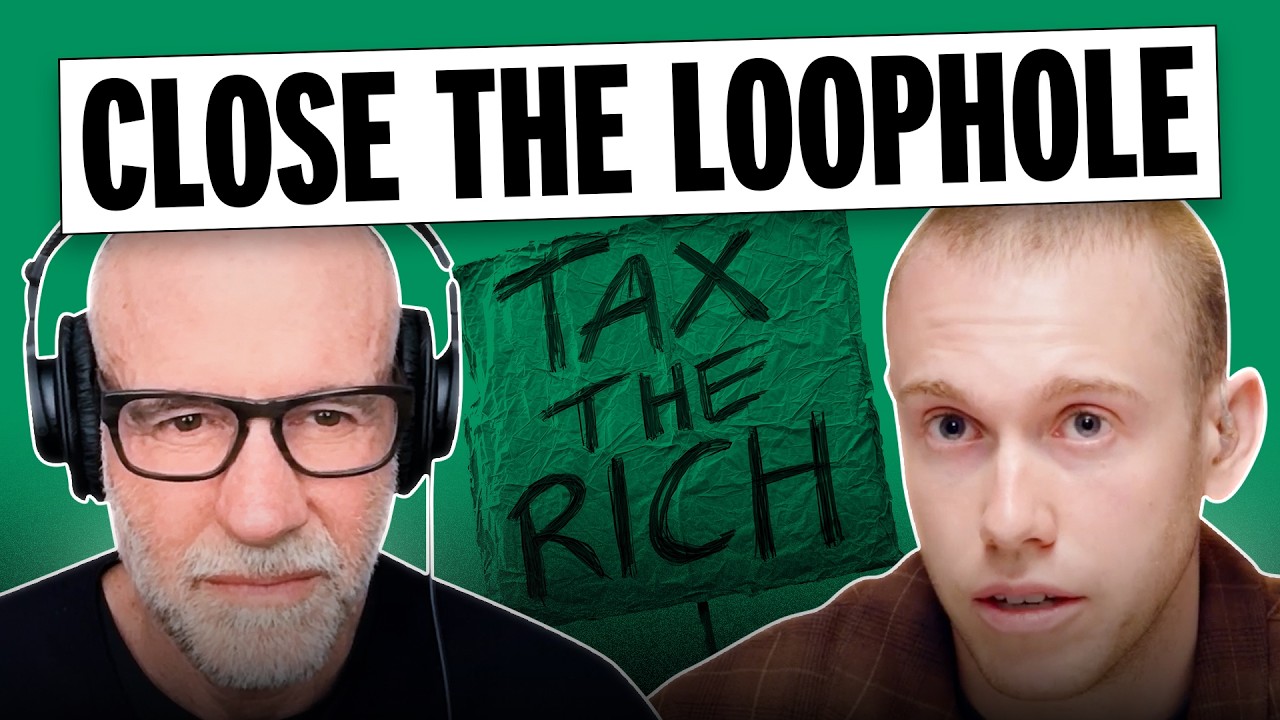
This hack was first made public way back in 2021
after the professors had informed Apple and Visa privately.
And to get to the bottom of why it's still possible,
we reached out to Apple,
and they didn't agree to an interview.
But here's what they said.
"This is a concern with the Visa system,
but Visa does not believe this kind of fraud
is likely to take place in the real world.
Visa has made it clear that their cardholders
are protected by Visa's zero liability policy."
This is exactly the same as their position
when the hack was first made public back in 2021.
So, it seems like Apple are basically saying,
"Well, this is a Visa problem."
So, we went and asked Visa what they thought.
- I think this specific vulnerability
is likely within a controlled setting.
Very unlikely from a scaled real world setting.
And then, kind of the last point
is from a consumer perspective,
is that in the cases where this is successful,
they have the ability to dispute this transaction
and get their refunds returned to them.
- I think that's fair.
You're saying it's not entirely scalable,
and then even if it does happen,
we'll give you your money back.
Like, that's a great, that's a great stance.
I still think though, a lot of people,
and I think our audience would really wanna hear
that you're actually making the technical changes
to stop this from ever happening again.
- 'Cause when you think about it from a scale perspective
and whether the network level defenses
that we have are effective in making sure
that this type of vulnerability is isolated,
we believe it is effective.
Because if it wasn't, you would hear a lot more data
about how this is an issue, and it simply isn't.
The point that I'm making is that you're never gonna be able
to completely eradicate any specific type of fraud
'cause it's going to exist, right?
- Yes. - What I'm saying
is that we have the right detections in place to ensure
that this type of fraud is not endemic.
- Would it not be even better
to just say this type of fraud is not possible.
Why not just say it's not probable?
Why not just totally get rid of it
by implementing an actual technical change?
- If you think about for every $100
of spend that occurs on card payments.
10 cents of that is lost to fraud.
So, every $100 it's 10 cents.
If you look at in-person transactions,
which is what kind of this topic
is really much more related to.
That number goes down to 2 cents
for every $100 of fraud that's being made.
- So, I've been thinking about this hack
and it reminds me a lot about people
who are afraid of flying.
Statistically, you're a lot more likely
to crash on the drive to the airport
than you are in the air.
So, I do understand Visa's argument generally.
Compared to other kinds of fraud,
this is just a drop in the ocean.
But airlines don't accept
a small number of crashes each year
as an inevitable cost of doing business.
No. Anytime there's a crash, they analyze it meticulously.
And then they do everything in their power
to make sure that it's never gonna happen again.
Visa says that they'll get you your money back
and that's great.
But you've still gotta notice the charge,
dispute it, and then wait.
Imagine waking up to see $10,000 gone from your account.
That's money for rent, insurance,
car payment, or a medical bill.
Even if the refund does come,
the stress before is gonna be very real.
So for me, the question is whether just saying
they're gonna refund it after the fact is good enough.
Or when a system touches the lives of so many people,
should we expect better?
One last thing.
We've been nominated for two Webby Awards.
One, for our video about the dangers of forever chemicals
and that's been nominated for best long form video.
The other one is about American football
and we did it with Tom Brady, and that's been nominated
for Best Creator to Creator Collaboration.
The thing is, when I checked last,
we were second place in voting for both of them.
So if you wanna help us out, you can go to the Webby website
and vote for us up till April 16th.
So if you do that, thank you very much.
That'll help us out a lot.
And as always, thank you for watching.
Okay, yeah. That's the whole demo.
I will now give you your money back.
- Yes.
- [Henry] Okay, we gotta.
Interactive Summary
Ask follow-up questions or revisit key timestamps.
In this video, Henry demonstrates a sophisticated cybersecurity hack to 'steal' $10,000 from MKBHD's locked iPhone. By collaborating with experts from the University of Surrey, they exploit a vulnerability in Apple's Express Transit Mode and Visa's payment processing. The video explains the technical details of the man-in-the-middle attack, which involves tampering with unencrypted transaction data to bypass security layers. Despite being known since 2021, the loophole remains unfixed, with Apple and Visa offering differing perspectives on its risk and responsibility.
Suggested questions
3 ready-made promptsRecently Distilled
Videos recently processed by our community